Social Media IO Roundup
This project is focused on identifying possible State-Sponsored Information Operations (IO) across various Social Media platforms.
“Having federal officials, whether judges, bureaucrats, or congressmen, impose a new definition of marriage on the people is an act of social engineering profoundly hostile to liberty.”
-Ron Paul
——
Review:
Social Media IO: Persona 101
Wrap up:
For this release we will cover the following:
Why would you use a Pen name?
What is a digital footprint?
What is a VPN?
What is a VPS?
What is a proxy?
What is TOR?
What is 2FA?
What is a Character?
Where to buy social media accounts?
Social Media IO: Behavioral Characteristics: Analysis of potential Actor(s) Part 1
Wrap up:
For this release we will cover the following:
Introduction to User Behavioral Analysis(UBA) and Social Networking Analysis(SNA).
Overview of Behavior Analysis.
Social Network Analysis fundamentals.
Data visualization Examples (Russian disinformation).
Network visualizations (how to look at the data)
——
Watch First:
Social engineering is one of the biggest threats to our organizations as attackers use manipulation techniques to coerce people into revealing secrets about our companies to allow attackers to gain access to critical systems. In this talk, we will look at some of the techniques used in social engineering and look at how to guard yourself against them. We will cover subjects like pre-texting, elicitation, and body language as techniques for manipulating people.
Mind manipulation techniques used by marketing masters The best strategies to use NLP and succeed in any action How to predict people’s behavior and influence their decisions And so much more! While mind control may seem abstract, it’s a skill you can acquire and practice. When used for good, manipulation helps us and the world move faster!
TIMESTAMPS:
Chapter 1: What is dark psychology 44:04 Chapter 2: Understanding psychological manipulation 1:00:06 Chapter 3: Understanding manipulation tactics and schemes 1:14:10 Chapter 4: Different manipulative personalities 1:32:08 Chapter 5: A walk through the body language and how it works with manipulation 1:43:32 Chapter 6: Development stages of manipulation 2:01:52 Chapter 7: How to spot manipulators and manipulative predators 2:40:27 Chapter 8: Identifying manipulative behaviors 3:05:13 Chapter 9: Dealing with manipulation in a relationship 3:34:22
Ever wanted to get into Social Engineering (SE), but thought you needed to know body language, facial expressions, be charming, and outgoing to succeed? This is a common misconception and you don’t need to know or be those things to make a start in SE. I think most SE talks focus on the more technical “human” aspects and I’m purposefully ignoring that side.
Academic-turned-cop and best-selling author George Doc Thompson describe how tactical language allows leaders to achieve their goals. Daniel Ames, the Sanford C. Bernstein & Co. Associate Professor of Leadership and Ethics, confirms that managing conflict is a critical predictor of leadership success and shows how what works in the streets converges with recent findings in social science. The workshop was part of the Program on Social Intelligences Science Meets Practice series, which pairs hands-on leadership training with breaking insights in psychology research.
Robert Cialdini published his book “Influence: The Psychology of Persuasion” in 1984. In it, he explores factors that affect the decisions that people make, particularly in relation to sales and purchasing. His work is an influential precursor to Nudge Theory, and its dark sibling, Sludge.
At the core of his work is the now well-accepted idea that decision-making is effortful, so individuals use a lot of rules of thumb and decision making shortcuts (heuristics) when deciding what to do, how to behave, or what action to take in any situation.
MEAT & POTATOES:
Social Media IO: Social Engineering 101
Goal:
For this release we will cover the following:
What is Social Engineering?
What is Phishing?
What is Smishing?
What is Vishing?
What is impersonation?
What are props?
What is psychological manipulation?
What are Cialdini's 6 Principles of Persuasion?
What is pretexting?
What is Quid pro quo?
What is the life cycle of the social engineering process?
Terms, Video reference of definitions and their function:
Definitions are necessary - yet we need to understand how it/things work.
Social Engineering: Social engineering is the art of manipulating people so they give up confidential information. The types of information these criminals are seeking can vary, but when individuals are targeted the criminals are usually trying to trick you into giving them your passwords or bank information, or access your computer to secretly install malicious software–that will give them access to your passwords and bank information as well as giving them control over your computer.
Criminals use social engineering tactics because it is usually easier to exploit your natural inclination to trust than it is to discover ways to hack your software. For example, it is much easier to fool someone into giving you their password than it is for you to try hacking their password (unless the password is really weak). [https://www.webroot.com/us/en/resources/tips-articles/what-is-social-engineering]
Phishing: A potential cybercrime in which a target or targets are contacted by email, telephone, or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking, and credit card details, and passwords.
The information is then used to access important accounts and can result in identity theft and financial loss. [https://www.phishing.org/what-is-phishing]
Smishing: utilizes our text messaging service which is technically called short message service or SMS. It seems that many people are more likely to trust a message that comes into their messaging app on their phone than with messages within an email. It seems difficult for many people to imagine that the hacker has their phone number. The truth is that it is easier to get to someone’s phone number than their email. There is a finite number of options with phone numbers. In the US a phone number is 10 digits where an email is not limited in size, there is a reasonable number of expected characters, but they can include numbers and alphanumeric characters (a, b, c, etc.) and symbols (!, #, %, etc.). There is a great deal more work just guessing email addresses than guessing at phone numbers. [https://www.trendmicro.com/en_us/what-is/phishing/smishing.html]
Vishing: is the use of telephony (often Voice over IP telephony) to conduct phishing attacks.
Landline telephone services have traditionally been trustworthy; terminated in physical locations known to the telephone company, and associated with a bill-payer. Now however, vishing fraudsters often use modern Voice over IP (VoIP) features such as caller ID spoofing and automated systems (IVR) to impede detection by law enforcement agencies. Voice phishing is typically used to steal credit card numbers or other information used in identity theft schemes from individuals. [https://en.wikipedia.org/wiki/Virtual_private_server]
Impersonation: No matter how secure a system is, there's always a way to break in. Hackers and malicious social engineers are turning to the weakest part of the infrastructure – the people – who are often the easiest to manipulate and deceive.
Impersonation is one of several social engineering tools used to gain access to a system or network in order to commit fraud, industrial espionage or identity theft. Impersonation differs from other forms of social engineering because it occurs in person, rather than over the phone or through email.
The social engineer "impersonates" or plays the role of someone you are likely to trust or obey convincingly enough to fool you into allowing access to your office, to information, or to your information systems. This type of social engineering plays on our natural tendencies to believe that people are who they say they are and to follow instructions when asked by an authority figure. It involves the conscious manipulation of a victim to obtain information without the individual realizing that a security breach is occurring. [https://mysecurityawareness.com/article.php?article=384&title=what-is-impersonation-in-social-engineering#.YI4Zf7VKjIU]
CON: A confidence trick is an attempt to defraud a person or group after first gaining their trust. Confidence tricks exploit victims using their credulity, naïveté, compassion, vanity, irresponsibility, and greed. Researchers have defined confidence tricks as "a distinctive species of fraudulent conduct ... intending to further voluntary exchanges that are not mutually beneficial", as they "benefit con operators ('con men') at the expense of their victims (the 'marks')".[https://en.wikipedia.org/wiki/Confidence_trick)]
Psychological Manipulation: Is a type of social influence that aims to change the behavior or perception of others through indirect, deceptive, or underhanded tactics.[1] By advancing the interests of the manipulator, often at another's expense, such methods could be considered exploitative and devious.
Social influence is not necessarily negative. For example, people such as friends, family, and doctors, can try to persuade to change clearly unhelpful habits and behaviors. Social influence is generally perceived to be harmless when it respects the right of the influenced to accept or reject it and is not unduly coercive. Depending on the context and motivations, social influence may constitute underhanded manipulation. [https://en.wikipedia.org/wiki/Psychological_manipulation]
Cialdini's 6 Principles of Persuasion: Influence, the classic book on persuasion, explains the psychology of why people say "yes"—and how to apply these understandings. Dr. Robert Cialdini is the seminal expert in the rapidly expanding field of influence and persuasion. His thirty-five years of rigorous, evidence-based research along with a three-year program of study on what moves people to change behavior has resulted in this highly acclaimed book.
You'll learn the six universal principles, how to use them to become a skilled persuader—and how to defend yourself against them. Perfect for people in all walks of life, the principles of Influence will move you toward profound personal change and act as a driving force for your success. [The book]
Pretexting: Is a type of social engineering attack that involves a situation, or pretext, created by an attacker in order to lure a victim into a vulnerable situation and to trick them into giving private information, specifically information that the victim would typically not give outside the context of the pretext. In its history, pretexting has been described as the first stage of social engineering and has been used by the FBI to aid in investigations. A specific example of pretexting is reverse social engineering, in which the attacker tricks the victim into contacting the attacker first. [https://en.wikipedia.org/wiki/Pretexting]
Quid pro quo: Is a Latin phrase used in English to mean an exchange of goods or services, in which one transfer is contingent upon the other; "a favor for a favor". Phrases with similar meanings include: "give and take", "tit for tat", "you scratch my back, and I'll scratch yours", and "one hand washes the other". Other languages use other phrases for the same purpose. [https://en.wikipedia.org/wiki/Quid_pro_quo]
The life cycle of Social Engineering: Starts from the Investigation of identifying the victims, gathering information, and selecting attack methods via phishing emails or calls. The second process is called a Hook which means deceiving the victim(s) to gain a foothold by the engine the target and taking control of the interaction. For example in phishing emails, when an attacker engages a victim with a fake job promotion in the company and accepting it by clicking on the malicious link. The third process is called a Play in which the attacker executes the attack and gets the victim’s information. Also, the attackers send the ransomware attacks when the victims click on the malicious link and it spreads quickly all over the network of the victim. The last step is called an Exit which means after the successful attack by the Social Engineer, they close the interaction by removing all traces of malware and covering tracks so that they won’t get caught. . [SE lifecycle]
——
Ethical Hacking (NETLAB18):
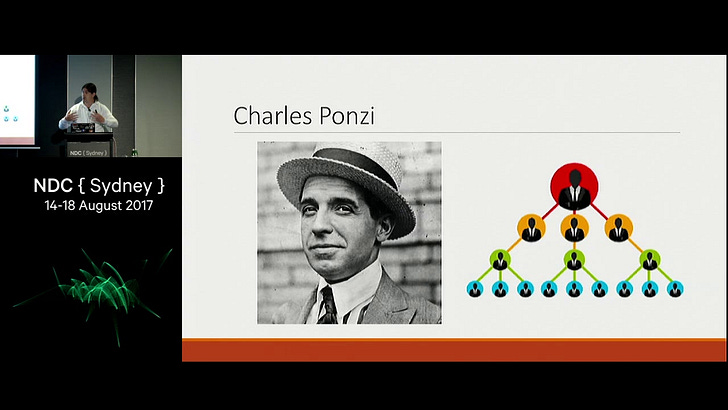
“I landed in this country with $2.50 in cash and $1 million in hopes, and those hopes never left me.” “Even if they never got anything for it, it was cheap at that price. Without malice aforethought I had given them the best show that was ever staged in their territory since the landing of the Pilgrims!
-Charles Ponzi
Follow the labs:
A series of google searches will give you the materials to follow along… enjoy
https://www.netdevgroup.com/content/cybersecurity/labs/ndg_ethical_hacking.html
——
Read of the Week:
To Get Lost is to Learn the Way: An Analysis of Multi-Step Social Engineering Attacks on the Web
Abstract:
Web-based social engineering (SE) attacks manipulate users to perform specific actions, such as downloading malware and exposing personal information. Aiming to effectively lure users, some SE attacks, which we call multi-step SE attacks, constitute a sequence of web pages starting from a landing page and require browser interactions at each web page. Also, different browser interactions executed on a web page often branch to multiple sequences to redirect users to different SE attacks. Although common systems analyze only landing pages or conduct browser interactions limited to a specific attack, little effort has been made to follow such sequences of web pages to collect multi-step SE attacks. We propose StraySheep, a system to automatically crawl a sequence of web pages and detect diverse multi-step SE attacks. We evaluate the effectiveness of StraySheep’s three modules (landing-page-collection, web-crawling, and SE-detection) in terms of the rate of collected landing pages leading to SE attacks, the efficiency of web crawling to reach more SE attacks, and accuracy in detecting the attacks. Our experimental results indicate that StraySheep can lead to 20% more SE attacks than Alexa top sites and search results of trend words, crawl five times more efficiently than a simple crawling module, and detect SE attacks with 95.5% accuracy. We demonstrate that StraySheep can collect various SE attacks, not limited to a specific attack. We also clarify attackers’ techniques for tricking users and browser interactions, redirecting users to attacks. [https://search.ieice.org/bin/pdf_link.php?category=A&lang=E&year=2021&fname=e104-a_1_162&abst=]
——
Feedback:
Social Media IO Roundup is an effort charged with educating and bringing attention to the murky world of cyber information operations. Highlighting tradecraft, concerns trends, techniques, and raising questions to a sector many don’t see. I’m not all-knowing and want to improve the content, so I need you the readers to interact.
Drop a line:
Email: dominanceinformation@gmail.com Instagram @informationdominance
——
Closing:
The human interface will always be an attack vector at some point in the system you are looking at. There will usually be a technician, clerk, secretary, and or someone with access that can be talked to - that's what we will interface with… that’s what we will exploit.
Standby for more at a later date.
-Bob aka INFODOM


Great writeup!!! Thank you for sharing this. When 2-factor auth becomes easier to break we are in for real trouble.