Friday, December 16, 2022 // (IG): BB // Bubba3dPrints // Coffee for Bob
Ukrainian Organizations Hit with New Supply Chain Attack
FROM THE MEDIA: Software supply chain attacks are not slowing down, and researchers have uncovered a new example that targeted victims in Ukraine with malicious Windows installer files that were designed to gather and exfiltrate sensitive data from compromised machines. The campaign involved the threat actors hosting the malicious files on torrent sites hosted in Russia and Ukraine. The files were disguised as legitimate installers for Windows 10 and researchers at Mandiant discovered the operation and attributed it to a new, unknown group it tracks as UNC4166. Though the actors are not known, Mandiant said some of the victim organizations overlapped with ones that APT28 has targeted previously with destructive malware attacks. APT28, also known as Fancy Bear, is associated with Russia’s GRU military intelligence unit.
READ THE STORY: DUO
NSA cyber director warns of Russian digital assaults on global energy sector
FROM THE MEDIA: National Security Agency Cyber Director Rob Joyce said Thursday he remains concerned about significant cyberattacks from Russia, warning that Moscow could unleash digital assaults on the global energy sector in the coming months. “I would not encourage anyone to be complacent or be unconcerned about the threats to the energy sector globally,” Joyce said. “As the [Ukraine] war progresses there’s certainly the opportunities for increasing pressure on Russia at the tactical level, which is going to cause them to reevaluate, try different strategies to extricate themselves.”
READ THE STORY: Cyberscoop
Russian hackers claim to have infiltrated FBI with names and bank details exposed
FROM THE MEDIA: Russian hacker group KillNet has claimed to have infiltrated the FBI in a massive cyber-attack on the US security agency. The pro-Kremlin group has reportedly posted online capturing to have stolen the personal data of more than 10,000 US federal agents. KillNet's attack is as yet unverified but the group claim's the data hacked includes social media passwords and bank details. Screenshots shared by the group of Telegram appear to boast of access to passwords from online stores, medical ID cards, and Google, Apple, and Instagram accounts. All passwords from online stores to the mass acceptance card, Google, and Apple accounts are at our disposal," read a statement attributed to the hackers on Russian Telegram channels.
READ THE STORY: Express (UK)
Spyware and surveillance-for-hire industry ‘growing globally’: report
FROM THE MEDIA: The spyware and surveillance-for-hire industry is “indiscriminately” targeting journalists, activists and political opposition, and growing on a global scale, the social media company Meta warned. In a new report published Thursday, the company said it has “continued to investigate and take actions against spyware vendors around the world, including in China, Russia, Israel, the United States and India, who targeted people in about 200 countries and territories.” Meta was one of the first to publicly challenge the spyware industry back in 2019, when it began legal proceedings against Israeli firm NSO Group for hacking into approximately 1,400 WhatsApp users’ mobile devices.
READ THE STORY: The Record
Ukraine’s Secret Weapon Is Ordinary People Spying on Russian Forces
FROM THE MEDIA: Ukraine—During Russia’s occupation of the southern Ukrainian city of Kherson, a large electronics store served Russian forces as a field hospital, barracks and storehouse for food. One morning last summer, Ukrainian forces struck the store, completely destroying it. It was one of numerous attacks that day on Russian-controlled territory deep inside the Kherson region. Before the blast, a small group of local Ukrainian activists had been sending photographs of the location and coordinates of the Russians over an encrypted Telegram channel to the Ukrainian military. That intelligence helped Ukrainian forces target the site, according to a military official who worked with such groups.
READ THE STORY: WSJ
Russia-Ukraine war reaches dark side of the internet
FROM THE MEDIA: In April, German police, acting on a tip-off from their American colleagues, discovered the servers of the single-largest online bazaar for narcotics and other contraband on the planet. From 2017, Hydra had dominated the illegal drug business in Russia and neighbouring countries. After taking control of the site, German authorities retrieved 23 million euros ($16.7m) in ill-gotten cryptocurrency. But what likely caught the attention of Western law enforcement was not Russian drug dealers, doing business mainly in Russia. Hydra also offered forged documents, hacking, and money laundering services, which could be used nefariously against Western interests or citizens.
READ THE STORY: Alijazeera
Ukrainian govt networks breached via trojanized Windows 10 installers
FROM THE MEDIA: Ukrainian government entities were hacked in targeted attacks after their networks were first compromised via trojanized ISO files posing as legitimate Windows 10 installers. These malicious installers delivered malware capable of collecting data from compromised computers, deploying additional malicious tools, and exfiltrating stolen data to attacker-controlled servers. One of the ISOs pushed in this campaign was hosted on the toloka[.]to Ukrainian torrent tracker by a user created in May 2022.
READ THE STORY: Bleeping Computer // Mandiant
The U.N. is sending Ukrainians aid in crypto. Should it?
FROM THE MEDIA: The United Nations said Thursday it will start aiding people displaced by Russia’s war in Ukraine with cryptocurrency. The organization’s refugee agency, the Office of the U.N. High Commissioner for Refugees (UNHCR), which often sends funds to those displaced from their homes for things like rent, food and heat, will transfer USD Coin (USDC) — a cryptocurrency pegged to the U.S. dollar and considered a stable coin — to uprooted Ukrainians who can ultimately exchange it for cash at MoneyGram locations worldwide. Proponents said it will help displaced people get money quicker and limit loss or theft in transit — but some skeptics say that adding another layer to getting aid at a time when the cryptocurrency market is in upheaval could be problematic and risky.
READ THE STORY: The Washington Post
FBI seizes 48 domains linked to DDoS-for-hire services: six charged in connection
FROM THE MEDIA: On Wednesday, the U.S. Department of Justice (DoJ) announced[1] that they had seized 48 domains that offered DDoS services to other potential cybercriminals. Six suspects have also been charged for their part in operating the “Stresser” or “Booter” platforms, which lowered the threshold for malicious activity and made it easier for anyone to commit these crimes. The FBI has shut down websites that allowed users to illegally pay for DDoS attacks. These types of attacks overload the target computer with information, which then gets “booted” from the internet (hence the name). Stresser platforms use identical functionality of DDoS features, although they are meant for genuine testing of the web service reliability. FBI has determined that these services were fake and were indeed used for malicious purposes instead.
READ THE STORY: 2 Spyware
Google drops TrustCor certificates as questions loom
FROM THE MEDIA: Google Thursday joined Mozilla and Microsoft in dropping TrustCor Systems as a root certificate authority. In Mozilla's dev-security-policy group, a public email discussion about certificate authority (CA) policies and governance, Google announced that "Due to a loss of confidence in its ability to uphold these fundamental principles and to protect and safeguard Chrome's users," the company would no longer support TrustCor certificates beginning with Chrome 111. The beta release of the browser is scheduled for Feb. 9, and the stable release is scheduled for March 7. Google's announcement follows decisions from Mozilla and Microsoft late last month to remove TrustCor from the root stores of their respective browsers.
READ THE STORY: TechTarget
Twitter’s war on bots cuts off users, Indonesia criminalizes online dissent, and US bill could block TikTok
FROM THE MEDIA: Rumors of Ukraine disappearing from Twitter have been popping up online this week. There have been credible reports that phone numbers with a Ukrainian country code are suddenly not recognized on the platform, leaving people who use two-factor authentication iced out. Although we could submit to the wicked notion that this is Musk trying to influence the war in Russia’s favor, it may just be a result of Twitter’s “war on bots.” Platformer reported that Twitter recently blocked traffic from 30 mobile carriers around the world, including some from Russia, in a (mostly failed) effort to snuff out spammers that temporarily cut off hundreds of thousands of users.
READ THE STORY: .Coda
Tracking Malicious Glupteba Activity Through the Blockchain
FROM THE MEDIA: Threat actors are increasingly leveraging blockchain technology to launch cyberattacks. By taking advantage of the distributed and decentralized nature of blockchain, malicious actors can exploit its anonymity for a variety of attacks, ranging from malware propagation to ransomware distribution. The Glupteba trojan is an example of a threat actor leveraging blockchain-based technologies to carry out their malicious activity. In this blog, Nozomi Networks Lab presents our latest findings on Glupteba and how security teams can search for malicious activity in the blockchain.
READ THE STORY: Security Boulevard
Chinese MirrorFace APT group targets Japanese political entities
FROM THE MEDIA: ESET researchers recently discovered a spear-phishing campaign targeting Japanese political entities and attributed it to the Chinese-speaking APT group tracked as MirrorFace. The experts tracked the campaign as Operation LiberalFace, it aimed at Japanese political entities, especially the members of a specific political party. The campaign was launched in June 2022, the spear-phishing messages were used to spread the LODEINFO backdoor, an implant used to deliver additional payloads, and exfiltrate the credentials and sensitive data from the victims. The researchers also detailed the use of a previously undescribed credential stealer named by ESET as MirrorStealer.
READ THE STORY: Security Affairs
Australian state hacker preparing “digital tribunal” for Putin’s cyberarmy
FROM THE MEDIA: Speaking with Ekonomichna Pravda, Australian state hacker and CEO of the Internet 2.0 cybersecurity company Robert Potter said that its possible to punish Russian hackers attacking Ukraine on the the Kremlin’s orders. “A digital tribunal is possible. We know the names of the leaders of Russian hacker communities. We are working on legal regulation and documentation of Russian cybercrime crimes. Australia has had positive experience prosecuting hackers in Nigeria and Vietnam. Russia is more difficult – we have no contact point with the Russian government.
READ THE STORY: Euromaidan Press
DPRK likely to focus on building 'three axes' of its weapons system next year: expert
FROM THE MEDIA: North Korea is likely to push forward with the development of its strategic and tactical nuclear weapons as well as reconnaissance satellites next year as Pyongyang seeks to strengthen its nuclear and missile capabilities, according to an expert Friday. "For the goal of the North Korean version of possessing 'two bombs and one satellite,' the North is likely to develop the three axes (of its weapons system) -- intercontinental ballistic missiles (ICBMs), submarine-launched ballistic missiles (SLBMs) and reconnaissance satellites," Hong Min, a researcher at the state-run Korea Institute for National Unification (KINU), said.
READ THE STORY: YNA
Microsoft Expanding 'Airband' Broadband Initiative Across Africa Via Satellite
FROM THE MEDIA: Microsoft aims to get another 10 million people online by linking two kinds of wireless connectivity: one to cover the first 22,000 or so miles, another to bridge the last several miles. The company announced(Opens in a new window) this new partnership with longstanding satellite-broadband operator Viasat Tuesday at the US-Africa Leaders Summit in Washington. This first addition of a satellite service to its Airband connectivity initiative(Opens in a new window) will bring internet access to 5 million people across Africa by 2025, with the other 5 million in Central and North America.
READ THE STORY: PCMAG
NSA warns Citrix devices are under attack from Chinese hackers, so update now
FROM THE MEDIA: The US National Security Agency (NSA) is warning that a hacking collective backed by the Chinese state is exploiting a zero-day security flaw in two common Citrix products to gain access to networks. The critical vulnerability, CVE-2022-27518(opens in new tab), affects the application delivery controller Citrix ADC and remote access tool Citrix Gateway, with both popular in business tech stacks. In an official blog post(opens in new tab), Peter Lefkowitz, chief security and trust officer at Citrix claimed that “limited exploits of this vulnerability have been reported,” but did not elaborate on the number of attacks or the industries involved.
READ THE STORY: TechRadar
Microsoft revised CVE-2022-37958 severity due to its broader scope
FROM THE MEDIA: Microsoft revised the severity rate for the CVE-2022-37958 vulnerability, the IT giant now rated it as “critical” because it discovered that threat actors can exploit the bug to achieve remote code execution. The CVE-2022-37958 was originally classified as an information disclosure vulnerability that impacts the SPNEGO Extended Negotiation (NEGOEX) security mechanism. The SPNEGO Extended Negotiation Security Mechanism (NEGOEX) extends Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) described in [RFC4178].
READ THE STORY: Security Affairs
Why the Twitter Files actually matter
FROM THE MEDIA: Big surprise: The Twitter Files — the reports based on internal Twitter documents and messages that the company’s new owner Elon Musk provided to journalists — have landed as a polarizing salvo in the culture war. Many inclined to distrust what they see as Big Tech’s liberal leanings have cried vindication. The documents show in detail how Twitter made key content moderation decisions that disadvantaged Trump, conservatives, and people who broke with the public health consensus on Covid-19. They say the evidence proves that, again and again, Twitter intervened to squelch speech that the liberal establishment didn’t like.
READ THE STORY: VOX
North Korean Spies Try New Hacking Method
FROM THE MEDIA: Daniel DePetris is a foreign affairs expert based in the United States. He received an email in October from Jenny Town, the director of 38 North, asking him to write about North Korea. But Town did not send the email. The sender was a suspected North Korean spy, cybersecurity researchers said. Instead of infecting DePetris’ computer and stealing important information, the sender appeared to be trying to get his thoughts on North Korean security issues. Cybersecurity researchers told Reuters news agency the email is part of a new campaign by a suspected North Korean hacking group. They said the group is targeting leading experts in foreign countries to better understand Western policy on North Korea.
READ THE STORY: VOA
Use of Tracking Technology- Walking the Regulatory Line (PDF)
FROM THE MEDIA: Across industries, organizations have deployed online tracking technologies, supplied by third-party vendors, on websites and mobile applications, to collect and analyze information about user behavior and enhance the user experience. Many organizations also rely on these technologies to ensure their websites and applications are functioning properly and to provide crash reports when users encounter issues, thereby playing an integral role in reducing downtime and timely addressing other website access and operational issues, as discussed further below. Tech giants such as Google1 and Meta, the parent company of Facebook,2 offer these technology services, which also include cookies, web beacons or tracking pixels, session replay scripts, and fingerprinting scripts, to organizations who may choose to embed them in the code of the organizations’ websites and applications.
READ THE STORY: Ropes & Gray
Automating Threat Intelligence Enrichment
FROM THE MEDIA: Recent events have given us a better idea of what cyber defeat looks like, and it’s not pretty. Whether it’s a data breach that costs an average of $4.24 million, a political leader targeted by hacking or government data being compromised – the stakes are high. Cybersecurity teams need to understand what malicious actors and hacking techniques are headed their way and what to do about them. We are starting to get a much better idea of what a cyber defeat looks like, and it’s not pretty. In response, the cybersecurity field developed threat intelligence, which focuses on identifying threats before they become breaches.
READ THE STORY: Security Boulevard
State-sponsored economic cyber-espionage for commercial purposes on the rise
FROM THE MEDIA: State-sponsored and cyber-enabled theft of intellectual property is on the rise as countries employ all means at their disposal to gain advantages in a global environment increasingly shaped by strategic rivalry and political mistrust. This is a conclusion we reach in our new ASPI report, State-sponsored economic cyber-espionage for commercial purposes: tackling an invisible but persistent risk to prosperity.
READ THE STORY: ASPI
Data breach hits Victoria’s revenue office
FROM THE MEDIA: The State Revenue Office of Victoria, the department responsible for administering the state’s taxation system, has suffered a data breach and a hacker group is offering to sell the data online. The attack follows a spate of data breaches and hacks at major Australian companies in recent months, most prominently telecommunications giant Optus and insurer Medibank. TPG Telecom also revealed this week that someone had broken into email servers to prowl for users’ cryptocurrency information. The SRO confirmed to The Australian Financial Review that it had suffered a “cyber incident involving a third-party provider”, but assured that “no customer data is involved” in the breach.
READ THE STORY: AFR
Ukraine Adapts To Power Cuts, Blunting Russia's Attacks On The 'Energy Front'
FROM THE MEDIA: When fuses blew and the music stopped at a rave party at the techno club Otel on the first weekend in December, shaven-headed men stripped to the waist and quirkily dressed women in sunglasses didn’t miss a beat, dancing on to their own rhythmic chants. As the wall of sound crumbled after each short-circuit of the generator, the crowd shouted “Putin is a d***head” -- a slogan that originated among soccer fans in 2014 and became more widespread following Russia’s invasion in February -- and waited, undaunted, for the power and the pulse to return.
READ THE STORY: Radio Free Europe Radio Liberty
FuboTV says World Cup streaming outage caused by a cyberattack
FROM THE MEDIA: FuboTV has confirmed that a streaming outage preventing subscribers from watching the World Cup Qatar 2022 semifinal match between France and Morocco was caused by a cyberattack. At approximately 2 PM ET, as users were getting ready to watch the World Cup semifinal, FuboTV subscribers found that they could not log in to the streaming service. Instead, they were greeted with a CB_ERR_OPEN error, stating "ff: downstream not available," when attempting to log in. Subscribers could not contact support to report the problem, as it requires a user to first log in to the FuboTV site, which could no longer be done.
READ THE STORY: Bleeping Computer
Charges dropped against French company that sold spyware to Egypt
FROM THE MEDIA: A Paris court yesterday dismissed charges of complicity in torture against a French company and its directors who sold advanced spyware to the Egyptian government. Nexa Technology and four of its executives were accused in 2021 of selling the Cerebro software to Egypt, which enabled the regime of President Abdel Fattah Al-Sisi to spy on political opponents, possibly torturing and forcibly disappearing them. However, the Paris Court of Appeal dropped the charges against Chairman Olivier Bohbot and CEO Stephane Salies among others, but did not order the case to be closed, meaning the investigation will continue.
READ THE STORY: MEMO
Unit 42 highlights threat intelligence importance as Russia, Ukraine ransomware attacks fly under the radar
FROM THE MEDIA: As threat actors continue to become more sophisticated, staying ahead of the curve is a game-changer. Threat intelligence is now more important than ever, because a perfect storm is brewing based on ransomware attacks between Russia and Ukraine, with nation-state actors undertaking significant cyber espionage work undetected, according to Wendi Whitmore (pictured), senior vice president for Unit 42 at Palo Alto Networks Inc. “When it comes to just general espionage techniques, data exfiltration, intellectual property theft, those are going on now more than ever,” she said. “We’re under the landscape of a major war going on between Russia and Ukraine of ransomware attacks. That’s one of the key reasons why having threat intelligence is so important. It’s become even more important now, because these groups switch teams more frequently than NFL trades.”
READ THE STORY: SiliconAngle
Phishing attack uses Facebook posts to evade email security
FROM THE MEDIA: A new phishing campaign uses Facebook posts as part of its attack chain to trick users into giving away their account credentials and personally identifiable information (PII). The emails sent to targets pretend to be a copyright infringement issue on one of the recipient's Facebook posts, warning that their account will be deleted within 48 hours if no appeal is filed. The link to appeal the account deletion is an actual Facebook post on facebook.com, helping threat actors bypass email security solutions and ensure their phishing messages land in the target's inbox. The Facebook post pretends to be "Page Support," using a Facebook logo to appear as if the company manages it.
READ THE STORY: Bleeping Computer
Items of interest
LEGO Fixes Startling BrickLink Exploit That Could Allow Hackers To Hijack Accounts
FROM THE MEDIA: Back in October, a researcher at the cybersecurity firm Salt Security uncovered multiple security vulnerabilities in the LEGO BrickLink website that could have allowed hackers to hijack users’ accounts and arbitrarily read files on the the Amazon cloud server hosting the website. Upon making this discovery, the researcher promptly disclosed the vulnerabilities to the LEGO security team, which confirmed the presence of the vulnerabilities. LEGO then updated the BrickLink website to fix these vulnerabilities in early November, with Salt Labs providing confirmation that the vulnerabilities were no longer exploitable.
READ THE STORY: HotHardWare
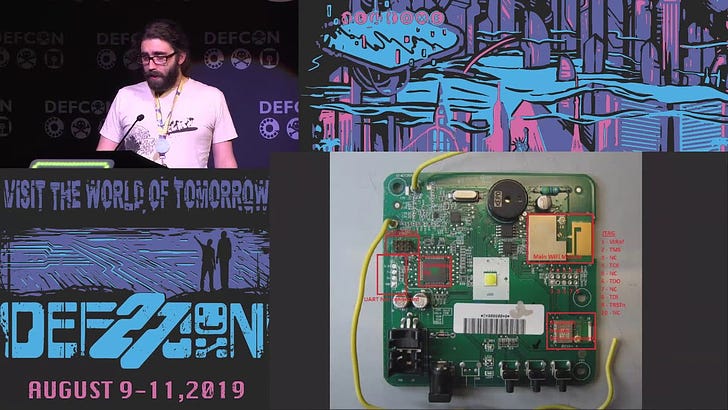
Philippe Laulheret - Intro to Hardware Hacking (Video)
FROM THE MEDIA: This talk is an introduction to hardware hacking and as a case study I’ll use the [REDACTED] Deskphone, a device frequently deployed in corporate environments. I’ll use it to introduce the tools and methodology needed to answer these questions.
Samy Kamkar's Crash Course in How to Be a Hardware Hacker (Video)
FROM THE MEDIA: Samy Kamkar is well known for many things, but lately it has been his hardware security hacks that have been turning heads. The nice thing to know is that, despite not having a background in hardware, Samy is able to run with the best of hardware researchers. At the Hackaday SuperConference he offered words of advice for anyone trying to walk the path of discovery with an exciting new piece of electronics. One might say it's a crash-course in how to be a hardware hacker.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com