Monday, June 13, 2022 // (IG): BB //New location: BOB's Newsletter
Linux malware ‘Symbiote’ used to attack Latin American financial sector
FROM THE MEDIA: Researchers at BlackBerry and Intezer have discovered a new Linux malware named “Symbiote” that is being used to target financial institutions across Latin America.
Joakim Kennedy, security researcher at Intezer, and the BlackBerry Research & Intelligence Team released a report last week highlighting the financially motivated campaign, noting that what makes Symbiote different from other Linux malware is that “it needs to infect other running processes to inflict damage on infected machines.”
READ THE STORY: The Record
Iranian Hackers Spotted Using a new DNS Hijacking Malware in Recent Attacks
FROM THE MEDIA: The Iranian state-sponsored threat actor tracked under the moniker Lyceum has turned to using a new custom .NET-based backdoor in recent campaigns directed against the Middle East.
"The new malware is a .NET based DNS Backdoor which is a customized version of the open source tool 'DIG.net,'" Zscaler ThreatLabz researchers Niraj Shivtarkar and Avinash Kumar said in a report published last week.
"The malware leverages a DNS attack technique called 'DNS Hijacking' in which an attacker-controlled DNS server manipulates the response of DNS queries and resolves them as per their malicious requirements."
READ THE STORY: THN
SentinelLabs uncovers decade-long cyber espionage operations by a Chinese threat group
FROM THE MEDIA: The notorious hacking group, Aoqin Dragon, primarily focuses on cyber-espionage targeting government, telecommunication, and educational organisations in Australia, Cambodia, Hong Kong, Singapore, and Vietnam.
“The threat actor has a history of using document lures with pornographic themes to infect users and makes heavy use of USB shortcut techniques to spread the malware and infect additional targets. Attacks attributable to Aoqin Dragon typically drop one of two backdoors, Mongall and a modified version of the open-source Heyoka project,” the research said.
Over the years, Aoqin Dragon has deployed three distinct infection chains. Between 2012 and 2015, it used Microsoft Office documents that exploited known vulnerabilities like CVE-2012-0158 and CVE-2010-3333. This was first identified by FireEye in 2014 in a spear-phishing campaign targeting an APAC government entity. The attack was coordinated by the Chinese-backed Naikon APT group.
READ THE STORY: TEISS
Hello XD Ransomware Installing Backdoor on Targeted Windows and Linux Systems
FROM THE MEDIA: Windows and Linux systems are being targeted by a ransomware variant called HelloXD, with the infections also involving the deployment of a backdoor to facilitate persistent remote access to infected hosts.
"Unlike other ransomware groups, this ransomware family doesn't have an active leak site; instead it prefers to direct the impacted victim to negotiations through Tox chat and onion-based messenger instances," Daniel Bunce and Doel Santos, security researchers from Palo Alto Networks Unit 42, said in a new write-up.
HelloXD surfaced in the wild on November 30, 2021, and is based off leaked code from Babuk, which was published on a Russian-language cybercrime forum in September 2021.
READ THE STORY: THN
People’s Republic of China State-Sponsored Cyber Actors Exploit Network Providers and Devices
FROM THE MEDIA: This joint Cybersecurity Advisory describes the ways in which People’s Republic of China (PRC) state-sponsored cyber actors continue to exploit publicly known vulnerabilities in order to establish a broad network of compromised infrastructure. These actors use the network to exploit a wide variety of targets worldwide, including public and private sector organizations. The advisory details the targeting and compromise of major telecommunications companies and network service providers and the top vulnerabilities—primarily Common Vulnerabilities and Exposures (CVEs)—associated with network devices routinely exploited by the cyber actors since 2020.
This joint Cybersecurity Advisory was coauthored by the National Security Agency (NSA), the Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI). It builds on previous NSA, CISA, and FBI reporting to inform federal and state, local, tribal, and territorial (SLTT) government; critical infrastructure (CI), including the Defense Industrial Base (DIB); and private sector organizations about notable trends and persistent tactics, techniques, and procedures (TTPs).
READ THE STORY: HSTODAY
Microsoft’s Bing Censors Politically-Sensitive Chinese Names in US Searches: Report
FROM THE MEDIA: Microsoft-owned search engine Bing is targeting politically sensitive Chinese names for censorship in the United States, according to research.
Citizen Lab, a cyber research center at the University of Toronto’s Munk School of Global Affairs, found that the censorship applied to Bing’s autosuggestion feature. Moreover, it impacts not only Bing but also the Windows Start menu search and DuckDuckGo, which share this same feature.
“We consistently found that Bing censors politically sensitive Chinese names over time, that their censorship spans multiple Chinese political topics, [and] consists of at least two languages, English and Chinese,” Citizen Lab stated in the report released on May 19.
READ THE STORY: The Epoch Times
Thanh Hoa, Vietnam Digitises Agricultural Activities
FROM THE MEDIA: For over a year, the Thanh Hoa province has been implementing digital transformation initiatives across its localities, in line with the Party Committee’s resolution that made digitisation an urgent and long-term strategic task.
In implementing the resolution, the provincial Farmers’ Union and Post Office signed a cooperative agreement to help farmers digitise the production and sale of farm produce and goods for the 2021-2025 period. So far, over 70% of the Farmers’ Union direction and guidance documents at the provincial and district levels are available online. Many agricultural products of the Union’s members have been introduced on two state-owned e-commerce platforms, namely, Postmart and Vo So.
The Union wants 4,000 households engaging in agro-forestry-fishery production, processing, and trading to offer their products on Postmart this year. The agency also plans to set up a showroom at the Farmer Support Centre. It will use ICT to enhance local farmers’ knowledge about digital technology and help them switch from traditional to digital agriculture.
READ THE STORY: Open Asia Gov
Saudi Warns of Ukraine War Exacerbating Cybersecurity Breaches
FROM THE MEDIA: Saudi experts are warning against aggravating cybersecurity breaches as the effects of the Russian-Ukrainian war take a toll. So far, Saudi efforts have led to adding 40 job roles for cadres working in the field of cybersecurity. Field specialists estimated the global shortage of human cadres at more than 3 million jobs. Saudi Arabia has become more in need of qualified human personnel due to the expansion of its technology market, which is close to a fifth of the entire market size in the Middle East.
A seminar on the national economic effects of cybersecurity showed that about 85% of cybersecurity problems are caused by human errors. However, cyber awareness and the use of technology and job examinations with human cadres can reduce these errors. Majed Al-Sahli, a specialist in strategy and international cooperation at the National Cybersecurity Authority (NCA), stressed that the national cybersecurity strategy reflects Saudi Arabia’s ambition in a balanced manner.
READ THE STORY: AAWSAT
Conti's Attack Against Costa Rica Sparks a New Ransomware Era
FROM THE MEDIA: FOR THE LAST two months, Costa Rica has been under siege. Two major ransomware attacks have crippled many of the country’s essential services, plunging the government into chaos as it scrambles to respond. Officials say that international trade ground to a halt as the ransomware took hold and more than 30,000 medical appointments have been rescheduled, while tax payments have also been disrupted. Millions have been lost due to the attacks, and staff at affected organizations have turned to pen and paper to get things done.
Costa Rica’s government, which changed midway through the attacks after elections earlier this year, has declared a “national emergency” in response to the ransomware—marking the first time a country has done so in response to a cyberattack. Twenty-seven government bodies were targeted in the first attacks, which ran from mid-April until the start of May, according to new president Rodrigo Chaves. The second attack, at the end of May, has sent Costa Rica’s health care system into a spiral. Chaves has declared “war” on those responsible.
READ THE STORY: Wired
Hackers are after SMEs’ digital estates. Here’s why you can’t overlook cyber security
FROM THE MEDIA: There are rarely second chances for SMEs in the cyber security game. In the US, the National Cyber Security Alliance published a study in 2012 showing that 60% of SMEs suffering a cyber incident didn’t survive beyond the following six months. While there has been progress in cyber security since then, cyber criminals have also grown more sophisticated and organized, and the truth is that one attack is enough to put a small company definitively out of business. And when they pull through, it is rarely unscarred.
SMEs can often display some complacency when it comes to cyber security, thinking that only large organizations are at risk, or that our remote island of Australia is not a strategic priority for hackers. That may have been true to an extent five years ago, but macroeconomic factors have put Australia under more cyber criminals’ radars, and studies show that small organizations with lower levels of preparedness to cyber attacks are low-hanging fruit for them.
READ THE STORY: Smart Company
Ag industry put on alert after series of cyberattacks
FROM THE MEDIA: A recent surge in cyberattacks on ag companies during critical planting and harvest seasons has prompted a warning from the FBI and efforts within the industry to develop stronger individual and shared defenses.
The agency pointed to ransomware attacks on six grain cooperatives during the fall harvest, plus two attacks earlier this year that could have hurt planting by disrupting seed and fertilizer supplies.
"Cyber actors may perceive cooperatives as lucrative targets with a willingness to pay due to the time-sensitive role they play in agricultural production," the FBI's April 20 notification stated.
READ THE STORY: Yahoo
Ukraine-Russia conflict generates sevenfold increase in international voice traffic
FROM THE MEDIA: At least 7 million+ refugees who have evacuated Ukraine since Russia’s invasion, as reported by the United Nations, generated unprecedented leap in inbound voice minutes.
Participating carriers such as BICS, BTS, iBasis, Orange, Tata Communications, Sparkle, Telefónica, and Telstra, contributed data on i3forum Insights. The platform is operated by TeleGeography.
Performance data is ingested into the system where it’s fully anonymized, 100% confidential, and completely secure. The data is then aggregated into an industry database that users can leverage to benchmark their own performance against the industry aggregate, i3forum says.
READ THE STORY: ITWire
Newly identified PACMAN flaw in Apple M1 CPU can't be patched
FROM THE MEDIA: Led by MIT's Mengjia Yan, researchers from MIT's Computer Science and Artificial Intelligence Laboratory (MIT CSAIL) created the novel attack using a combination of memory corruption and speculative execution to bypass the M1's security. The research team's proof of concept also demonstrated the attack's effectiveness against the CPU kernel, which could have far-reaching impacts on any PAC-enabled ARM system.
A PAC typically guards the OS kernel by causing any mismatch between a PAC pointer and its authentication code to result in a crash. The PACMAN attack's reliance on speculative execution and repeated guesses is critical to its success. Due to the finite number of PAC values, the team determined that it would be possible for a malicious actor to find the correct PAC value by simply trying them all. However, this requires the ability to make multiple guesses without triggering an exception any time the values are incorrectly guessed. The researchers figured out a way to do just that.
READ THE STORY: TechSpot
Hacking Ham Radio: Why It’s Still Relevant and How to Get Started
FROM THE MEDIA: This week we discuss hacking ham radio with special guests Caitlin Johanson, Rick Osgood, and Larry Pesce. In this episode you’ll learn what ham radio is, why its still relevant, why would attackers want to hack ham radio, all about packet radio and APRS (Automatic Packet Reporting System), and what equipment and licensing you need to get started in ham radio.
READ THE STORY: Security Boulevard
FDNY seeks firewall to stop doxxing, hacking of rescue workers’ personal data
FROM THE MEDIA: The FDNY is seeking to build a digital firewall to protect the Big Apple’s thousands of rescue workers from cyberattacks, including “doxxing,” The Post has learned.
The department recently put out a call in the City Record for consultant services “for the development and implementation of protective strategies to address the cyber threat of doxxing and to provide resiliency for the security of personal information.”
Doxxing is the publishing of personal information on the internet with the intent to bully, harass or threaten others.
The sick practice has become increasingly prevalent online. A radical pro-choice group recently doxxed six Supreme Court justices to spur protesters into showing up outside their homes to oppose overturning Roe v. Wade, the landmark ruling legalizing abortion.
READ THE STORY: NYPOST
Osmosis exploiters laundered $5 million
FROM THE MEDIA: Established in 2021, diffusion could be a decentralized exchange engineered And hosted on Cosmo blockchain. It’s a native utility token known as “OSMO” deployed last October. Diffusion is that, the latest crypto project to encounter a sudden attack, because the looters created away with $5 million. The past few weeks haven’t been simple for crypto projects, particularly exchanges. Not solely is the larger pessimistic market discouraging for them, however many cryptocurrency exchanges have additionally been within the eye of attacks and sexploitations. The Cosmo-based decentralized exchange (DEX), diffusion, is the latest crypto exchange to face a hack.
READ THE STORY: The Coin Republic
Website of Nagpur's Institute of Science hacked by 'DragonForce Malaysia' 'on insult of Prophet'
FROM THE MEDIA: The website of the Institute of Science, Nagpur was found hacked on Sunday with the hackers identifying themselves as 'DragonForce Malaysia' whose message on its home page read that "it is a special operation on the insult of our Prophet Mohammad", police said.
The restoration work of the website is going on, they said.
The hacking of the website occurred amid protests in parts of the country over the objectionable remarks made on Prophet Mohammad by now-suspended BJP spokesperson Nupur Sharma and expelled party leader Naveen Kumar Jindal.
Several countries, including Saudi Arabia, United Arab Emirates (UAE), Indonesia, Pakistan, Afghanistan, Jordan, Bahrain, Maldives, Malaysia, Oman, Iraq and Libya, have denounced their comments.
"The home page of the website carried a message in which people were urged to unite and start a campaign against India. The website was hacked through a malware. The hackers identified themselves as 'DragonForce Malaysia'," police inspector (Cyber) Nitin Phatangare said.
READ THE STORY: New Indian Express
Hacking Crypto Through Social Media
FROM THE MEDIA: Have you heard the one about the crypto investor who got hacked and lost all their Bitcoin? It’s true - cryptocurrency spam, hacks, and fraud are all on the rise. That means there’s an urgent need to think about the security risks to often-valuable digital investments. Bloomberg reporter Hannah Miller talks about the nature and scope of these hacks, and Ronghui Gu, chief executive officer of the blockchain security firm CertiK shares how to avoid them.
READ THE STORY: Bloomberg
Items of interest
FBI official: Chinese hackers boost recon efforts
FROM THE MEDIA: Chinese hackers have stepped up their probes against the U.S. tech sector since Russia’s invasion of Ukraine, an FBI official said on Thursday.
“We’ve actually seen — here in the San Francisco area — an uptick in reconnaissance from Chinese advanced persistent threat actors, specifically,” Elvis Chan, an assistant special agent in charge at the bureau’s San Francisco field office, said during a panel discussion at the RSA conference. He did not name any specific groups.
Chan, who manages the field office’s cyber branch, said Chinese hackers have increased their scans, in part, because they “want to see” how the U.S. and its private sector react to Moscow’s unprovoked assault on Ukraine.
“They’re still looking to steal as much intellectual property as they can,” he added, a nod to the longtime issue of the digital plundering by the Chinese that has been estimated to cost the U.S. billions of dollars annually.
He noted China’s COVID-19 vaccines “are nowhere near as good” as the ones produced by the U.S. and other Western nations, before adding that the perpetrators are “looking to steal proprietary information from our entire tech sector.”
The insight comes two days after the FBI — along with the NSA and the Cybersecurity and Infrastructure Security Agency (CISA) — issued an advisory that provided fresh details about how Chinese hackers have targeted, and compromised, major telecommunications companies and internet service providers by exploiting publicly known vulnerabilities.
Chan said that while top federal cyber officials are focused on the ongoing military conflict in Europe, “the Chinese government, the Iranian government, the North Korean government, none of them are sleeping” or halting their own malicious digital activities.
READ THE STORY: The Record
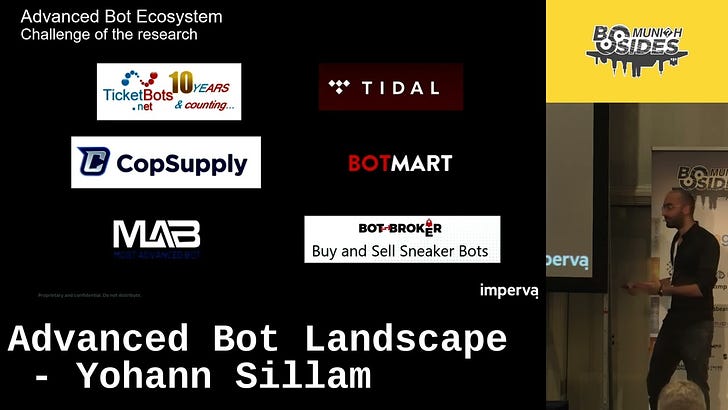
Advanced Bot Landscape - Yohann Sillam (Video)
FROM THE MEDIA: Bad bots traffic represents around a quarter of Internet traffic today and is predicted to increase. This traffic includes website content scanning, stolen credit card checking, denial of service, inventory.
Measuring Cyber Defense With The MITRE Framework - Marcus Osterloh (Video)
FROM THE MEDIA: The MITRE ATT&CK framework provides a common taxonomy for adversary behaviors. Based on this body of knowledge, detection capabilities can be measured, tracked and compared. These capabilities are often measured at an atomic level. However, real adversaries combine multiple steps in an attack flow. To address this MITRE created the Attack Flow project. Its goal is to develop a data format to describe the sequence of adversary behaviors.
About this Product
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com